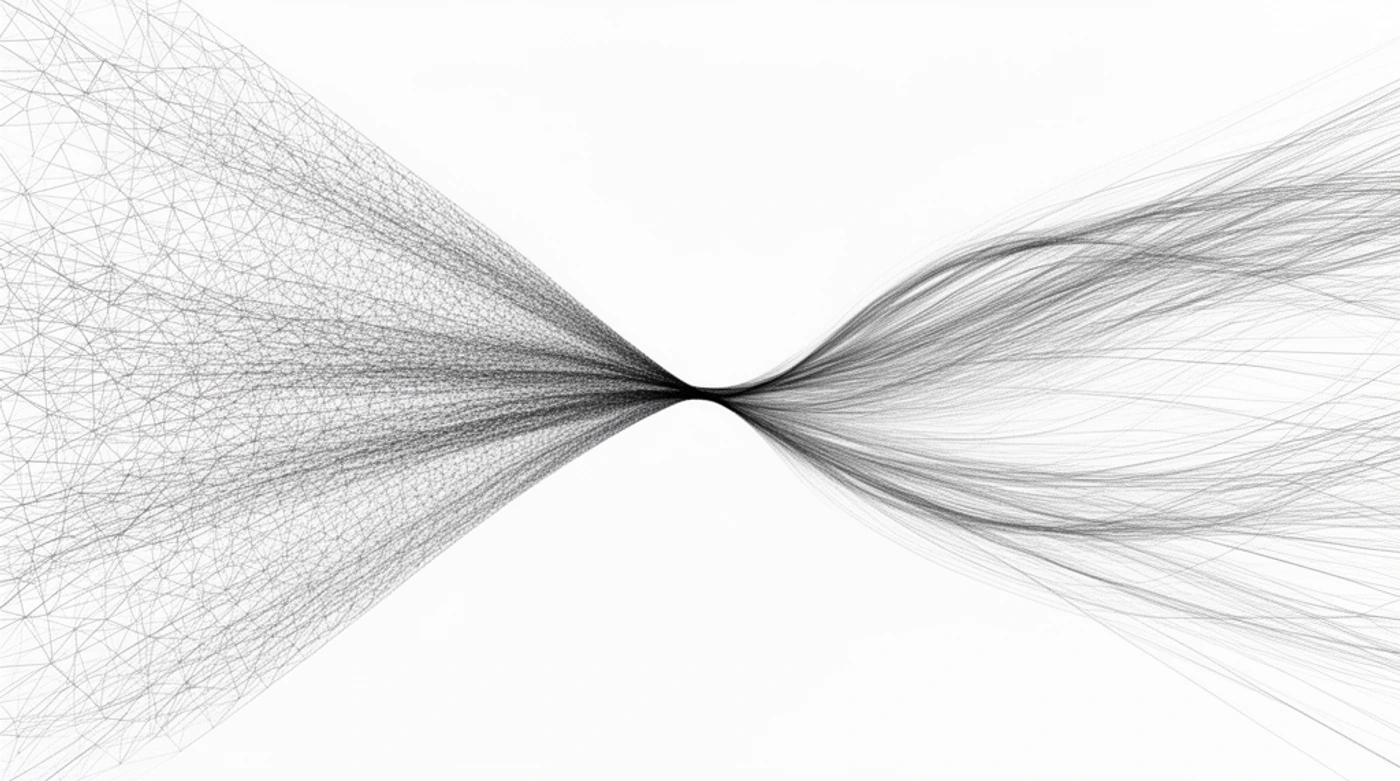
Most rate-limiting outages happen because teams picked an algorithm that did not match traffic shape.
Question
Which rate-limiting algorithm best fits my real traffic pattern?
Quick answer
Use:
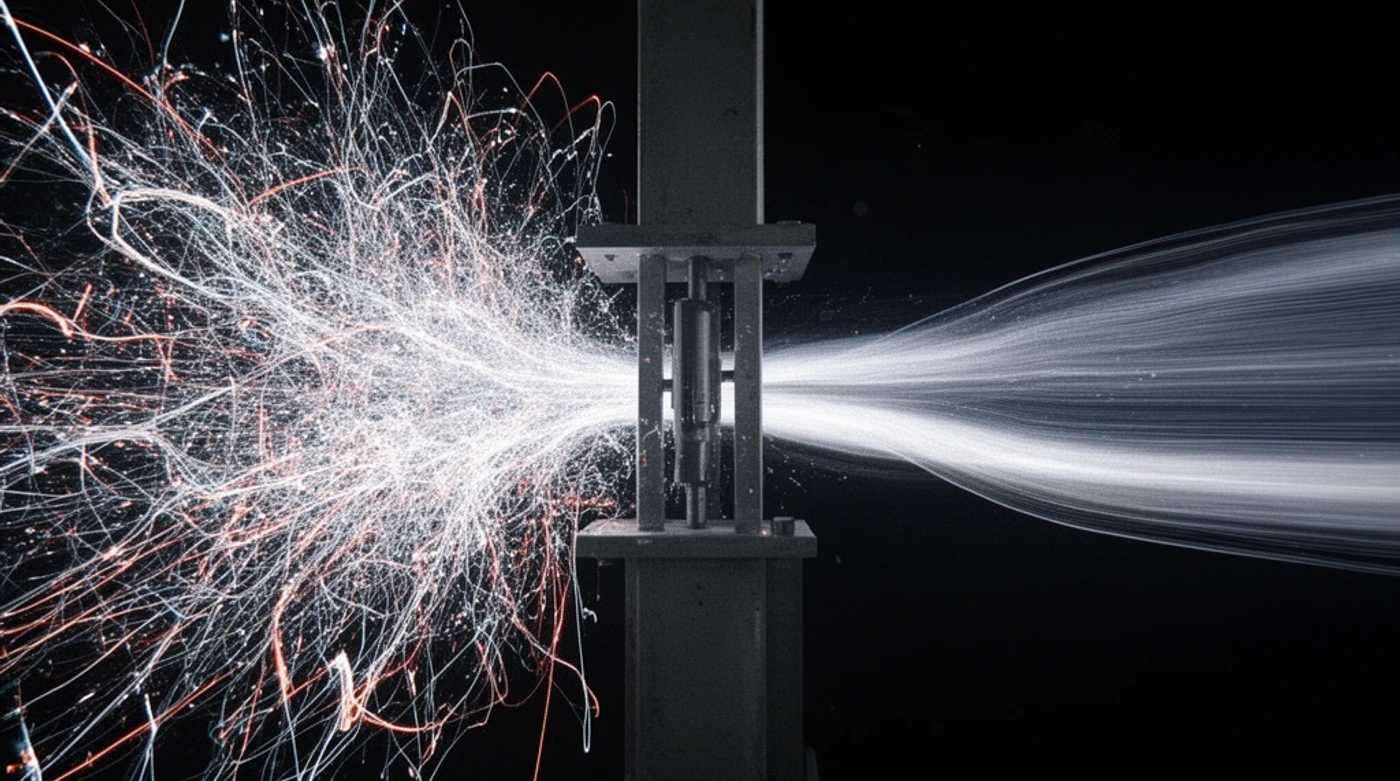
- Token bucket for burst tolerance with controlled average rate,
- Fixed window for simple low-cost internal limits,
- Sliding window when fairness precision matters.
Algorithm choice is a governance decision, not just a math choice.
Selection checklist
- Are bursts legitimate user behavior or mostly abuse?
- Do you need strict fairness across each minute/second boundary?
- What is your tolerance for enforcement jitter versus compute cost?
If fairness matters more than compute simplicity, avoid fixed window.
Common failure pattern
Teams start with fixed window because it is easy, then discover boundary effects that users experience as random throttling.
Algorithm fit table
| Algorithm | Best for | Tradeoff |
|---|---|---|
| Token bucket | Legitimate bursts with average-rate guardrails | Slightly less strict fairness |
| Fixed window | Simple low-cost internal controls | Boundary artifacts |
| Sliding window | User fairness and smoother enforcement | More compute/state overhead |
Pick based on traffic shape and fairness requirements, not implementation convenience.
10-minute action step
- Pick one high-traffic endpoint and one failure mode.
- Define the exact API contract behavior you expect under load.
- Simulate burst traffic and verify status codes, headers, and retry guidance.
- Document one contract invariant and enforce it in automated tests.
Success signal
Your team can predict failure behavior from the contract without checking production logs.