
Rate Limiting Is Not a Counter. It Is a Real-Time Governance System.
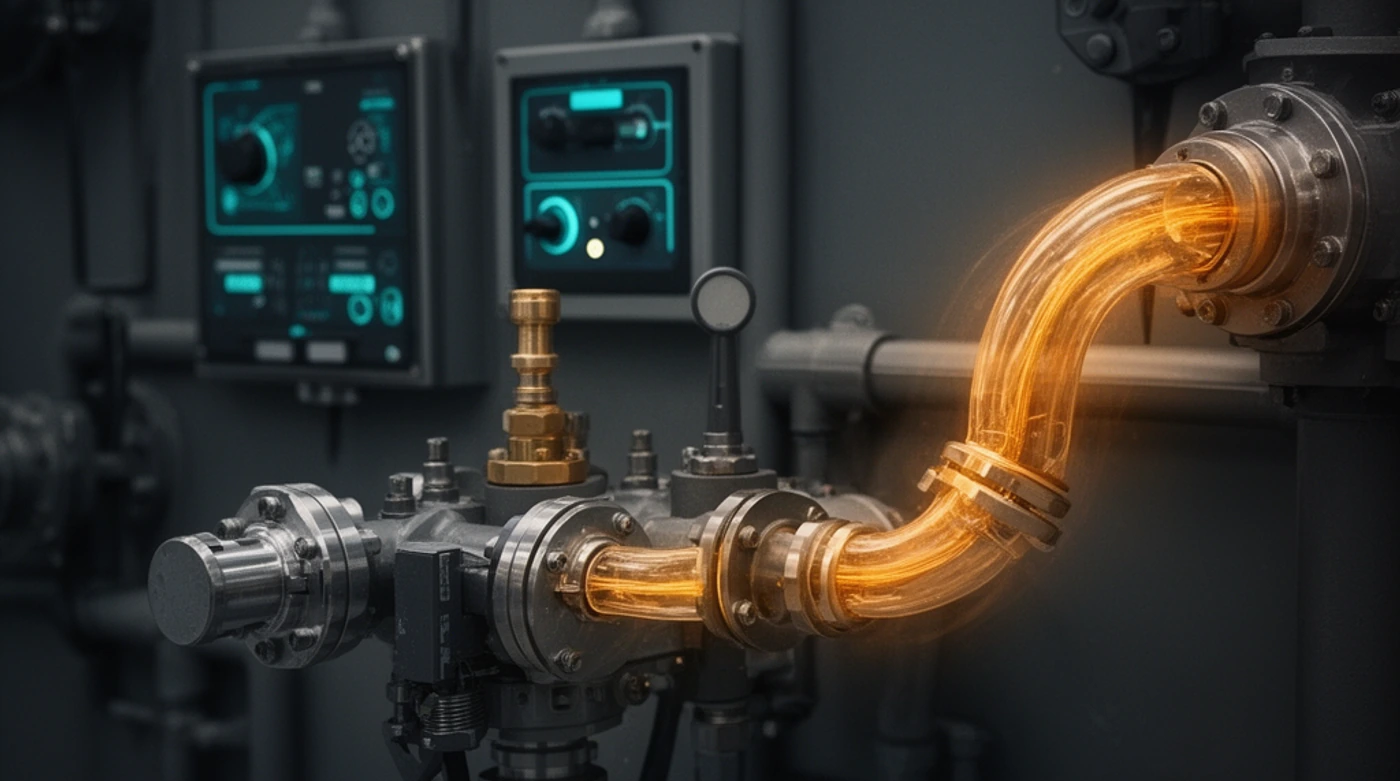
Rate limiting looks like arithmetic in tutorials, but in production it allocates scarce capacity, encodes fairness assumptions, and shapes client behavior under stress.
6 articles in this category.

Rate limiting looks like arithmetic in tutorials, but in production it allocates scarce capacity, encodes fairness assumptions, and shapes client behavior under stress.
Shadow AI is not primarily a compliance failure. It is what happens when capability arrives before permission, and when demand outruns an organization's ability to govern what is already being used.

A practical pre-engagement due diligence model for fractional CTO work that surfaces delivery, security, architecture, and governance risk without slowing momentum.

The market has shifted from AI assistants to AI agents with real permissions. With OpenClaw, Moltbook, OpenAI Frontier, and Claude Opus 4.6 all accelerating in early 2026, the key question is no longer capability. It is operational readiness and control.

If your AI product touches customer data, subprocessors are part of your architecture whether you planned for them or not. In 2026, understanding subprocessor agreements is no longer legal trivia - it is operational competence.

Explore how WebRTC uses DTLS and SRTP protocols to provide mandatory encryption for all communications, ensuring privacy and security in real-time applications.